Manually and accurately checking security holes
This company offers a service that extracts vulnerability hidden in web applications under the supervision of the leading web security expert, Hiroshi Tokumaru. In addition to the diagnosis covering "Learn Systematically How to Make a Secure Web Application" supported by many web professionals and the industry standard guideline, "OWASP TOP10 (2017 edition)", we can give a report that includes not only the result but also a modification method proposal by doing manual inspection performed by technical experts with development experience.
Profile of Mr. Hiroshi Tokumaru:
After joining Kyocera Corp. in 1985, he engaged in software development and planning. In 1999, he became interested in Web Application Security, inspired by the method design of authetication billing basis for mobile phones. In the year 2004, he commercialized the same field, and independently established HASH Consulting Inc. (Currently: EG Secure Solutions Inc.) in 2008. While doing vulnerability examination and consulting work, he is conducting security awareness program through blogs and workshops.
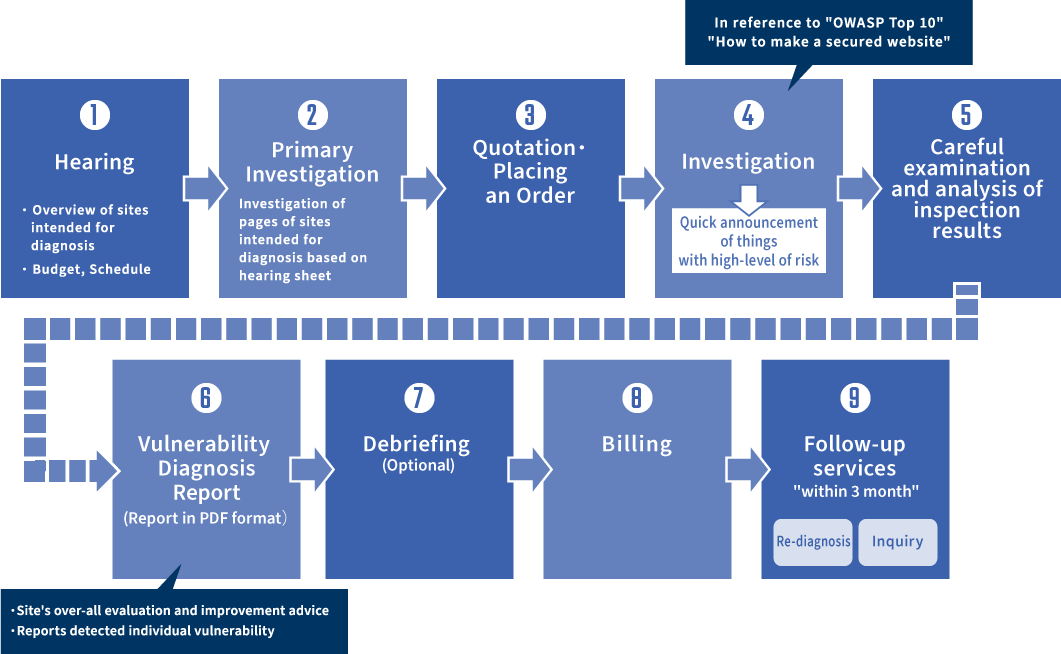
Business Flow Chart

Standard Examination
It is a basic examination that detects vulnerability by comprehensive examination while operating the web application to be examined. items to be emanined cover "OWASP TOP 10 (2017 edition)" and "How to Make a Safe Website".

Premium Examination
It is an examination which examines in more details. Since it checks specifications up to source codes, it can find the vulnerability of systems undetective on the surface, etc. It also covers items added in "OWASP Top 10" (2017 edition).

Examination of Web Health
A simple examination based on the specification worked out by the municipality security department of the local municipality Inforaiton Center. Speaking of simplified examination, in general, there are many cases that only a few basic components to be examined are included. However, Web Health Examination conducts an extensive investigation which covers 13 components.
Strengths and Points of Services
-
Manual Diagnosis by Skilled Technical Experts Specialized in Application Development
The distinction of this company's vulnerability diagnosis does not depend on diagnosis tool, but depends on manual diagnosis by skilled professional engineers specialized in Web Application Development. By doing manual diagnosis, it is possible to suggest repeatable special operations, and diagnosis and resolution method from the developer's point of view.
-
Examination Report and Debriefing Session based on the Countermeasures Proposal for Vulnerability
For vulnerability examination result, we are not just submitting a report, but we can also give a detailed explanation by holding a debriefing session where your company's security personnels will be gathered.
During a debriefing session, we are not just reading out the report, but we also explain about the countermeasure methods by type of vulnerability detected. Since we give advice based on our knowledge acquired from long years of experience in examination and latest security trends, we can raise the overall security measures.
Frequently Asked Questions
The Web Security Specialist will offer diagnostic plans based on the detailed hearing. We can quickly improve by intensively diagnosing misused functions and reporting the detected vulnerabilities together with concrete measures.
In improving vulnerability of a whole website, appropriate time is necessary. Therefore, as a countermeasure until the modification is completed, it is possible to propose using WAF, a defense function against vulnerability of web application.
In this company, we implement vulnerability diagnosis based on "OWASP Top 10", "How to Make a Safe Website", etc. We will create and submit reports based on the criterias above and contribute to earn the trust from users.
For Inquiries regarding Services and Quotations
